Newsletter
This is the latest edition - interesting & relevant information in byte sizes
Words From the Tech Desk
We have officially moved past the first quarter of the year - and it certainly started with a big bang. The months ahead present opportunity, but also important questions we cannot afford to ignore. How secure is the network I design, control, and support? Have I conducted a proper OT risk assessment? Do my deployments align with recognised cybersecurity standards?
Cybersecurity in Operational Technology is no longer optional or theoretical. It is measurable, auditable, and increasingly enforceable. Key frameworks define the landscape: ISA/IEC 62443 for industrial automation, NIST SP 800-82 for control systems, ISO/IEC 27001 for information security, NERC CIP for utilities, MITRE ATT&CK for behavioural detection, and IEC 61508 for functional safety. These span every vertical - building automation, energy, factory automation, oil and gas, rail, trackside, road systems, and water.
Across all sectors, one truth remains: many organisations believed they were secure until they discovered they were not. Security today must move beyond perimeter thinking. It requires visibility, segmentation, monitoring, lifecycle management, and a clear understanding of how AI is reshaping both defence and adversary sophistication. This is not about fear. It is about preparedness. Resilience is not built during an incident - it is engineered long before one occurs.
Onwards,
Anton van der Westhuizen
Tehran's Warning To Every South African Control Room

Industrial control systems are no longer just operational assets - they are strategic targets. What has already been proven in conflict environments now applies directly to everyday infrastructure.
The bombs fell on Tehran. The world saw the explosions. What it did not see was the operation that made them possible. Before aircraft entered Iranian airspace, cyber operations had already disabled the communications systems supporting air defence infrastructure. No radar response. No interception. No visibility. The systems did not explode. They stopped seeing.
Not Distant Geopolitics
This is not distant geopolitics. It is a technical reality that applies directly to industrial infrastructure everywhere. The control systems compromised in these operations share the same architectural foundations as those running substations, water treatment plants, ports, and transport networks. The same PLCs. The same protocols. The same assumptions about how systems behave.
The Fifteen-Year Arc
Over the past fifteen years, cyber operations have moved from disruption to precision. Stuxnet demonstrated that industrial processes could be manipulated while operators saw normal conditions. More recent campaigns show deeper capability - targeting engineering environments, exploiting protocol behaviour, and using industrial-native communication methods to remain undetected. In late 2024, researchers discovered IOCONTROL, a custom malware platform designed to compromise devices common across water, energy, and manufacturing environments. At discovery, it evaded all 66 antivirus engines on VirusTotal.
The South African Reality
At the same time, South Africa has experienced a measurable rise in cyber incidents affecting essential services, logistics, and public infrastructure. The Government Employees Pension Fund was breached. The Weather Service was taken offline. The National Health Laboratory Service had blood testing shut down. Transnet's 2021 cyber-attack exposed port fragility, disrupting national trade flows. These events rarely begin with dramatic failure. They begin quietly, in the network layer, long before operations are visibly affected.
The Shift That Matters
This is the shift that matters. Industrial infrastructure no longer fails only through physical faults. It fails when communications become unpredictable. When systems cannot see, they cannot respond. When they cannot respond, control is lost.
Assumptions That No Longer Hold
Many environments still rely on architectures designed for reliability, not for adversarial conditions. They assume stable behaviour, trusted communication, and predictable recovery. Those assumptions no longer hold. The lesson is not about fear. It is about recognition. Infrastructure is now a cyber-physical system. What affects the network affects the operation. Resilience is no longer defined by whether systems run. It is defined by whether they remain predictable when conditions change. That is the standard the next phase of infrastructure will demand.
When The Network Fails, The Tracks Go Dark

A signal aspect is only as reliable as the data that illuminates it. Rail operators invest heavily in rolling stock and permanent way. The communication layer between them often receives attention only when trains stop moving.
Signalling networks carry more than messages. They carry authority to proceed, interlocking permissions, and track occupancy status. When that data flow becomes intermittent - even for milliseconds - the system defaults to its safest state. Stopped.
The Fragile Handshake Between Field and Control
Track circuits continuously report presence. Axle counters validate train integrity. Interlockings confirm route availability. Each handshake depends on precise timing. A corrupted Ethernet frame, a ring reconvergence delay, or interference on a copper tail can break the logical circuit without breaking the physical one.
Operators see the symptom: a signal refuses to clear. The cause remains invisible inside the network.
Where Legacy Meets Modern Demand
Most rail communication networks evolved organically. Serial connections remain in critical paths. Fibre rings overlay copper tails. Ethernet switches designed for office environments attempt to survive traction power interference and vibration.
The result is predictable instability. Networks recover - eventually. But signalling does not wait for eventual.
The Coming Demands of High-Speed Rail
South Africa's high-speed rail programme is progressing under the Limpopo-Gauteng Speed Train Project, part of a broader R530 billion national initiative. Phase 1 prioritises the Gauteng-Limpopo-KwaZulu-Natal corridor, with dedicated high-speed lines capable of 250-300 km/h. Construction is expected to begin late 2026, with first services targeted for 2030.
This transformation demands more than new tracks. Trackside communication between high-speed trains and control depots must operate with precision that conventional signalling networks cannot deliver. Trains moving at 300 km/h require uninterrupted data handovers, deterministic latency, and redundancy that switches without interruption. The current communication layer - fragmented, legacy-dependent, and rarely stress-tested - will not support these speeds. If Joburg to Durban and Joburg to Polokwane are to operate high-speed services, the underlying network must adapt now, before the first rail is laid.
Designing for Predictable Recovery
Industrial networking designed for rail environments behaves differently. Deterministic ring protocols reconverge within defined windows. Redundant paths carry live traffic simultaneously, not standby until failure. Diagnostics preempt rather than report.
When an axle counter loses communication, the network should not require manual intervention to restore it. The architecture should re-establish the path within the signalling system's tolerance - without alarm floods, without operator confusion, without stopped trains.
The Question Every Rail Engineer Should Ask
If your signalling network lost power across three substations today and restored simultaneously, would behaviour be predictable? Would interlockings re-establish in sequence? Would controllers recognise devices in the correct order?
The answer determines whether your next outage lasts minutes or hours.
Reliability Is Designed. Instability Is Inherited.
Modern rail communication replaces chance with certainty. When the network becomes visible, the tracks stay dark only when intended - never by accident.
Security At The Edge is No Longer Optional

Industrial networks are now connected by design.
Substations, water plants, transport cabinets, distributed assets - all visible, all reachable. The question is no longer whether we are connected. It is whether we are protected at the edge. As operational technology converges with enterprise and cloud, the boundary between them disappears.
Why the Edge Is the New Risk Surface
OT protocols were engineered for reliability, not authentication. Once routed into corporate or remote-access environments, they operate without deep inspection or identity control. This is where exposure begins.
Security Cannot Be Bolted On
Dropping enterprise IT security into substations or field cabinets without considering electrical conditions, lifecycle expectations, and deterministic behaviour introduces instability. In OT, protection must coexist with predictable recovery.
The Westermo-Fortinet Integration
Westermo and Fortinet have partnered to integrate rugged industrial networking with enterprise-grade cybersecurity.
Westermo's WeOS-based switches and routers provide resilient Layer 2/3 communication in harsh environments. Fortinet's FortiGate NGFW, FortiAuthenticator, and FortiPAM add deep packet inspection, identity enforcement, and privileged access control.
For digital substations, Welotec enables virtualised FortiGate deployment on IEC 61850-3 rugged servers - reducing hardware sprawl while increasing protocol-level inspection.
The result is coordinated IT/OT security at the edge. Not layered complexity.
Key Point
Connectivity without OT-aligned cybersecurity is unmanaged exposure. The organisations strengthening their edge architecture now will define the reliability of tomorrow's infrastructure.
Did You Know?
Future-proof connectivity is not about speed - it is about frequency diversity.
The Westermo Merlin 3100 supports 450 MHz, LTE, and 5G within the same platform, allowing networks to prioritise coverage (450 Mhz), availability (LTE), or bandwidth (5G) depending on the application and environment.
Cybersecurity certification at component level accelerates system approval.
The Viper 3000 series achieves IEC 62443-4-2 SL2 certification, meaning authentication, integrity, and access control are built into the device, reducing the effort required to certify the full system under IEC 62443-3-3
“Rugged” in rail networking includes cybersecurity, not just hardware.
The Viper 3000 is engineered for vibration, temperature extremes, and electrical stress - but equally for secure boot, hardened OS behaviour, and long lifecycle resilience, reflecting the shift from safety-only to safety + security design in OT environments.
Modernisation does not require shutdown - if done correctly.
ProSoft enables phased upgrades where legacy PLCs (PLC-5, SLC, DH+, Remote I/O) remain operational while new systems are introduced, allowing parallel operation, data bridging, and gradual migration without full rip-and-replace downtime.
Modernize Without The Rip-and-Replace

Legacy automation equipment does not fail because it is obsolete. It fails because the world around it moved on. The challenge is modernising without sacrificing the programming, logic, and operational continuity that keep production running.
When engineers hear "modernisation," they visualise extended downtime and the disruption of a full rip-and-replace. There is a better way. Phased modernisation updates systems on your timeline and your budget - minimising operational impact while extending asset life.
The Legacy Challenge
Allen-Bradley PLC-5 and SLC platforms remain in service because they are reliable. The problem is connectivity. These systems were designed for Remote I/O, DH+, and Df1 - protocols that do not speak EtherNet/IP, OPC UA, or MQTT. Getting legacy device data into modern control systems or enterprise analytics platforms is essential. Without it, the Industrial Internet of Things remains inaccessible from the assets that generate the most operational value.
Bridging Old and New
ProSoft gateways enable phased modernisation by allowing legacy equipment to communicate with modern controllers without rewriting original PLC code. This approach extends asset life by retaining functional I/O and field devices, connects legacy protocols such as Remote I/O and DH+ to EtherNet/IP, and reduces downtime by modernising in stages rather than all at once.
Phased Modernisation in Practice
PanelView terminals can upgrade from Remote I/O and DH+ to new EtherNet/IP PanelView Plus terminals without changes to the PLC program. FLEX I/O adapters transition to EtherNet/IP while maintaining existing field wiring. CompactLogix controllers can manage existing Remote I/O devices through a gateway supporting up to 32 racks of I/O. For DF1 equipment, replacement solutions now enable phased migration following Rockwell Automation's discontinuation of the 1761-NET-ENI.
Key Takeaway
Legacy equipment does not need to be abandoned to be modernised. With protocol translation and phased migration, you protect original programming, preserve operational continuity, and gain the connectivity required for IIoT and enterprise visibility. The question is no longer whether to modernise. It is whether you control the timeline or the timeline controls you.
Meet Us at Africa Automation Indaba 2026
Africa Automation Indaba 2026 is a focused, executive-level forum designed for meaningful engagement between decision-makers and a select group of exhibitors. This is not a high-volume trade show. It is a two-day environment where conversations shape direction.
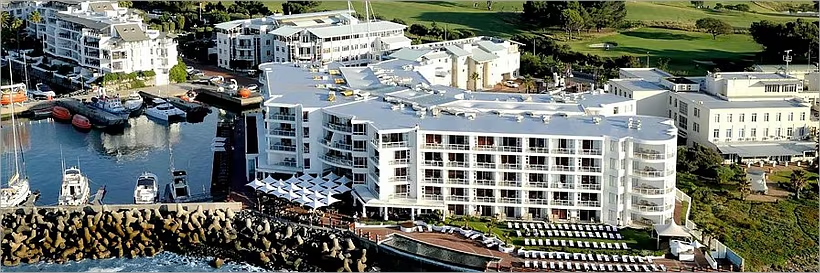
Taking place on 13-14 May 2026 at the Radisson Collection Hotel, Waterfront, Cape Town, the Indaba brings together government, industry leaders, engineers, and technology innovators to address automation investment, AI readiness, IIoT, robotics, and smart manufacturing across Africa.
Presentations and discussions over the two days are intended to inform and influence the next phase of industrial transformation on the continent.
Throughput Technologies will be exhibiting, and joined by Westermo, for direct engagement with attendees. Our participation reflects a clear commitment to the industry and to the role industrial communications plays in enabling reliable, secure infrastructure.
The format prioritises dialogue over presentation. That is where the value lies. If you are attending, we invite you to connect. If you are considering it, understand this: the people in the room are there to engage - and to make decisions.

